
Security News
PodRocket Podcast: Inside the Recent npm Supply Chain Attacks
Socket CEO Feross Aboukhadijeh discusses the recent npm supply chain attacks on PodRocket, covering novel attack vectors and how developers can protect themselves.
@igor-lemon/javascript-deobfuscator
Advanced tools
A simple but powerful deobfuscator to remove common JavaScript obfuscation techniques. Open an issue if there is a feature you think should be implemented.
A simple but powerful deobfuscator to remove common JavaScript obfuscation techniques. Open an issue if there is a feature you think should be implemented.
Online version at deobfuscate.io
See bottom for more complicated example with features chained together.
Before
const a = ['\x20', '\x57\x6f\x72\x6c\x64', '\x48\x65\x6c\x6c\x6f'];
console.log(a[2] + a[0] + a[1]);
After
console.log("Hello" + " " + "World");
Before
function a(b, c) {
return someFunction(b, c);
}
const result = a(5, 6);
After
const result = someFunction(5, 6);
Before
function a(b, c) {
return c + 2 * b;
}
const result = a(5, 6);
After
const result = 6 + 2 * 5;
Before
function a(b, c) {
return c + 2 * b;
}
function b(c, d) {
return a(c, d);
}
function c(d, e) {
return b(d, e);
}
const result = c(5, 6);
After
const result = 6 + 2 * 5;
Before
let total = 0x2 * 0x109e + -0xc * -0x16a + -0x3234;
for (let i = 0x1196 + 0x97b * 0x3 + -0x2e07; i < -0x95 * -0x38 + -0x1a75 + -0x619; i++) {
total += i;
}
After
let total = 0;
for (let i = 0; i < 10; i++) {
total += i;
}
Before
console.log('He' + 'll' + 'o' + ' Wo' + 'r' + 'ld');
After
console.log("Hello World");
All these features can be chained together to simplify code.
Before
const ar = ['\x48\x65\x6c\x6c\x6f', 0x95, '\x20', 0x1a75, '\x57\x6f\x72\x6c\x64', -0x53, '\x6c\x6f\x67']
const a = function(b, c) {
return c + 2 * b;
}, b = function(c, d) {
return a(c, d);
}, c = function(d, e) {
return b(d, e);
};
const message = ar[0] + ar[2] + ar[4];
const result = c(ar[1] * 0x38 + ar[3] + 0x619, 0x12 * ar[5] + 0x1a13 + 0x621);
console[ar[6]](message + ' ' + result);
After
const message = "Hello World";
const result = 40106;
console.log(message + " " + result);
Often obfuscated scripts don't just use an array of strings, instead they have string decoder functions that execute more complex logic, such as the example below.
function _0x29e92(_0x337a9) {
const _0x38a2db = ['\x48\x65\x6c\x6c\x6f', '\x20', '\x57\x6f\x72\x6c\x64'];
const _0x9ca21 = _0x337a9 - 0x1;
const _0xa8291 = _0x38a2db[_0x9ca21];
return _0xa8291;
}
const _0x78e2 = _0x29e92(1) + _0x29e92(2) + _0x29e92(3);
console.log(_0x78e2);
To tell the deobfuscator to execute this function, you can use the "#execute" directive like so:
function _0x29e92(_0x337a9) {
"#execute";
const _0x38a2db = ['\x48\x65\x6c\x6c\x6f', '\x20', '\x57\x6f\x72\x6c\x64'];
const _0x9ca21 = _0x337a9 - 0x1;
const _0xa8291 = _0x38a2db[_0x9ca21];
return _0xa8291;
}
const _0x78e2 = _0x29e92(1) + _0x29e92(2) + _0x29e92(3);
console.log(_0x78e2);
The deobfuscator will then evaluate this function and attempt to replace any calls to it with the correct values:
const a = "Hello World";
console.log(a);
A few important points about function evaluation:
Put the obfuscated script in input/source.js and run:
npm start
Or use the online version at deobfuscate.io
FAQs
A simple but powerful deobfuscator to remove common JavaScript obfuscation techniques. Open an issue if there is a feature you think should be implemented.
We found that @igor-lemon/javascript-deobfuscator demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Socket CEO Feross Aboukhadijeh discusses the recent npm supply chain attacks on PodRocket, covering novel attack vectors and how developers can protect themselves.

Security News
Maintainers back GitHub’s npm security overhaul but raise concerns about CI/CD workflows, enterprise support, and token management.
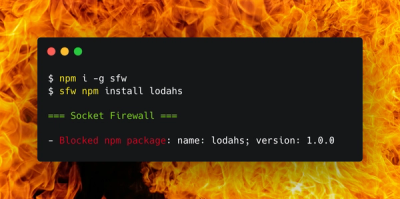
Product
Socket Firewall is a free tool that blocks malicious packages at install time, giving developers proactive protection against rising supply chain attacks.