
Product
Introducing License Enforcement in Socket
Ensure open-source compliance with Socket’s License Enforcement Beta. Set up your License Policy and secure your software!
@noble/secp256k1
Advanced tools
Fastest JS implementation of secp256k1. Independently audited, high-security, 0-dependency ECDSA & Schnorr signatures
@noble/secp256k1 is a JavaScript library for elliptic curve cryptography, specifically for the secp256k1 curve. It is commonly used in blockchain and cryptocurrency applications for key generation, signing, and verification.
Key Generation
This feature allows you to generate a random private key and derive the corresponding public key using the secp256k1 curve.
const secp = require('@noble/secp256k1');
const privateKey = secp.utils.randomPrivateKey();
const publicKey = secp.getPublicKey(privateKey);
console.log('Private Key:', privateKey);
console.log('Public Key:', publicKey);Signing
This feature allows you to sign a message using a private key. The message is an array of bytes, and the signature is generated using the secp256k1 curve.
const secp = require('@noble/secp256k1');
const message = new Uint8Array([1, 2, 3]);
const privateKey = secp.utils.randomPrivateKey();
const signature = secp.sign(message, privateKey);
console.log('Signature:', signature);Verification
This feature allows you to verify a signature using the corresponding public key and the original message. It returns a boolean indicating whether the signature is valid.
const secp = require('@noble/secp256k1');
const message = new Uint8Array([1, 2, 3]);
const privateKey = secp.utils.randomPrivateKey();
const publicKey = secp.getPublicKey(privateKey);
const signature = secp.sign(message, privateKey);
const isValid = secp.verify(signature, message, publicKey);
console.log('Is the signature valid?', isValid);Elliptic is a widely-used JavaScript library for elliptic curve cryptography. It supports multiple curves, including secp256k1. Compared to @noble/secp256k1, elliptic is more versatile but may be less optimized for performance in secp256k1-specific use cases.
Secp256k1 is a native Node.js binding to the secp256k1 library used in Bitcoin. It is highly optimized for performance but requires native compilation, which can be a drawback for some users. @noble/secp256k1, being a pure JavaScript implementation, is easier to use in browser environments.
BitcoinJS is a library for Bitcoin-related operations, including key generation, signing, and verification using secp256k1. While it offers a broader range of Bitcoin-specific functionalities, it is less focused on general elliptic curve cryptography compared to @noble/secp256k1.

Fastest JS implementation of secp256k1, an elliptic curve that could be used for asymmetric encryption, ECDH key agreement protocol and signature schemes. Supports deterministic ECDSA from RFC6979 and Schnorr signatures from BIP0340.
Audited with crowdfunding by an independent security firm. Tested against thousands of test vectors from a different library. Check out the online demo and blog post: Learning fast elliptic-curve cryptography in JS
noble-crypto — high-security, easily auditable set of contained cryptographic libraries and tools.
Use NPM in node.js / browser, or include single file from GitHub's releases page:
npm install @noble/secp256k1
// Common.js and ECMAScript Modules (ESM)
import * as secp from "@noble/secp256k1";
// If you're using single file, use global variable instead:
// nobleSecp256k1
(async () => {
// You pass a hex string, or Uint8Array
const privateKey = "6b911fd37cdf5c81d4c0adb1ab7fa822ed253ab0ad9aa18d77257c88b29b718e";
const message = "hello world";
const messageHash = await secp.utils.sha256(message);
const publicKey = secp.getPublicKey(privateKey);
const signature = await secp.sign(messageHash, privateKey);
const isSigned = secp.verify(signature, messageHash, publicKey);
// Sigs with improved security (see README)
const signatureE = await secp.sign(messageHash, privateKey, { extraEntropy: true });
// Malleable signatures, compatible with openssl
const signatureM = await secp.sign(messageHash, privateKey, { canonical: false });
// Supports Schnorr signatures
const rpub = secp.schnorr.getPublicKey(privateKey);
const rsignature = await secp.schnorr.sign(message, privateKey);
const risSigned = await secp.schnorr.verify(rsignature, message, rpub);
})();
To use the module with Deno, you will need import map:
deno run --import-map=imports.json app.ts
app.ts
import * as secp from "https://deno.land/x/secp256k1/mod.ts";
const publicKey = secp.getPublicKey(secp.utils.randomPrivateKey());
console.log(publicKey);
imports.json
{
"imports": {
"crypto": "https://deno.land/std@0.119.0/node/crypto.ts"
}
}
getPublicKey(privateKey)getSharedSecret(privateKeyA, publicKeyB)sign(msgHash, privateKey)verify(signature, msgHash, publicKey)recoverPublicKey(hash, signature, recovery)schnorr.getPublicKey(privateKey)schnorr.sign(hash, privateKey)schnorr.verify(signature, hash, publicKey)getPublicKey(privateKey)function getPublicKey(privateKey: Uint8Array | string | bigint, isCompressed = false): Uint8Array;
privateKey will be used to generate public key.
Public key is generated by doing scalar multiplication of a base Point(x, y) by a fixed
integer. The result is another Point(x, y) which we will by default encode to hex Uint8Array.
isCompressed (default is false) determines whether the output should contain y coordinate of the point.
To get Point instance, use Point.fromPrivateKey(privateKey).
getSharedSecret(privateKeyA, publicKeyB)function getSharedSecret(privateKeyA: Uint8Array | string | bigint, publicKeyB: Uint8Array | string | Point): Uint8Array;
Computes ECDH (Elliptic Curve Diffie-Hellman) shared secret between a private key and a different public key.
To get Point instance, use Point.fromHex(publicKeyB).multiply(privateKeyA).
To speed-up the function massively by precomputing EC multiplications,
use getSharedSecret(privateKeyA, secp.utils.precompute(8, publicKeyB))
sign(msgHash, privateKey)function sign(msgHash: Uint8Array | string, privateKey: Uint8Array | string, opts?: Options): Promise<Uint8Array>;
function sign(msgHash: Uint8Array | string, privateKey: Uint8Array | string, opts?: Options): Promise<[Uint8Array, number]>;
Generates low-s deterministic ECDSA signature as per RFC6979.
It's strongly recommended to pass {extraEntropy: true} to improve security of signatures:
k generation. Exposing k could leak private keyssign arguments:
msgHash: Uint8Array | string - message hash which would be signedprivateKey: Uint8Array | string | bigint - private key which will sign the hashoptions?: Options - optional object related to signature value and formatoptions?.recovered: boolean = false - whether the recovered bit should be included in the result. In this case, the result would be an array of two items.options?.canonical: boolean = true - whether a signature s should be no more than 1/2 prime order.
true makes signatures compatible with libsecp256k1,
false makes signatures compatible with openssloptions?.extraEntropy: Uint8Array | string | true - additional entropy k' for deterministic signature, follows section 3.6 of RFC6979. When true, it would automatically be filled with 32 bytes of cryptographically secure entropyoptions?.der: boolean = true - whether the returned signature should be in DER format. If false, it would be in Compact format (32-byte r + 32-byte s)The function is asynchronous because we're utilizing built-in HMAC API to not rely on dependencies.
signSync counterpart could also be used, you need to set utils.hmacSha256Sync to a function with signature key: Uint8Array, ...messages: Uint8Array[]) => Uint8Array. Example with noble-hashes package:
const { hmac } = require('@noble/hashes/hmac');
const { sha256 } = require('@noble/hashes/sha256');
secp256k1.utils.hmacSha256Sync = (key: Uint8Array, ...msgs: Uint8Array[]) => {
const h = hmac.create(sha256, key);
msgs.forEach(msg => h.update(msg));
return h.digest();
};
// Can be used now
secp256k1.signSync(msgHash, privateKey)
verify(signature, msgHash, publicKey)function verify(signature: Uint8Array | string, msgHash: Uint8Array | string, publicKey: Uint8Array | string): boolean
function verify(signature: Signature, msgHash: Uint8Array | string, publicKey: Point): boolean
signature: Uint8Array | string | { r: bigint, s: bigint } - object returned by the sign functionmsgHash: Uint8Array | string - message hash that needs to be verifiedpublicKey: Uint8Array | string | Point - e.g. that was generated from privateKey by getPublicKeyoptions?: Options - optional object related to signature value and formatoptions?.strict: boolean = true - whether a signature s should be no more than 1/2 prime order.
true makes signatures compatible with libsecp256k1,
false makes signatures compatible with opensslboolean: true if signature == hash; otherwise falserecoverPublicKey(hash, signature, recovery)function recoverPublicKey(msgHash: Uint8Array | string, signature: Uint8Array | string, recovery: number): Uint8Array | undefined;
msgHash: Uint8Array | string - message hash which would be signedsignature: Uint8Array | string | { r: bigint, s: bigint } - object returned by the sign functionrecovery: number - recovery bit returned by sign with recovered option
Public key is generated by doing scalar multiplication of a base Point(x, y) by a fixed
integer. The result is another Point(x, y) which we will by default encode to hex Uint8Array.
If signature is invalid - function will return undefined as result.To get Point instance, use Point.fromSignature(hash, signature, recovery).
schnorr.getPublicKey(privateKey)function schnorrGetPublicKey(privateKey: Uint8Array | string): Uint8Array;
Returns 32-byte public key. Warning: it is incompatible with non-schnorr pubkey.
Specifically, its y coordinate may be flipped. See BIP340 for clarification.
schnorr.sign(hash, privateKey)function schnorrSign(msgHash: Uint8Array | string, privateKey: Uint8Array | string, auxilaryRandom?: Uint8Array): Promise<Uint8Array>;
Generates Schnorr signature as per BIP0340. Asynchronous, so use await.
msgHash: Uint8Array | string - message hash which would be signedprivateKey: Uint8Array | string | bigint - private key which will sign the hashauxilaryRandom?: Uint8Array — optional 32 random bytes. By default, the method gathers cryptogarphically secure entropyschnorr.verify(signature, hash, publicKey)function schnorrVerify(signature: Uint8Array | string, msgHash: Uint8Array | string, publicKey: Uint8Array | string): boolean
signature: Uint8Array | string | { r: bigint, s: bigint } - object returned by the sign functionmsgHash: Uint8Array | string - message hash that needs to be verifiedpublicKey: Uint8Array | string | Point - e.g. that was generated from privateKey by getPublicKeyboolean: true if signature == hash; otherwise falseutils.randomBytes(): Uint8ArrayReturns Uint8Array of 32 cryptographically secure random bytes.
Uses crypto.web.getRandomValues in browser, require('crypto').randomBytes in node.js.
utils.randomPrivateKey(): Uint8ArrayReturns Uint8Array of 32 cryptographically secure random bytes that can be used as private key. The signature is:
(key: Uint8Array, ...msgs: Uint8Array[]): Uint8Array;
utils.bytesToHex(bytes: Uint8Array): stringConverts a byte array to hex string.
utils.sha256 and utils.hmacSha256Asynchronous methods that calculate SHA256 and HMAC-SHA256. Use browser built-ins by default.
utils.sha256Sync and utils.hmacSha256SyncThe functions are not defined by default, but could be used to implement signSync method (see above).
utils.precompute(W = 8, point = BASE_POINT): PointReturns cached point which you can use to pass to getSharedSecret or to #multiply by it.
This is done by default, no need to run it unless you want to disable precomputation or change window size.
We're doing scalar multiplication (used in getPublicKey etc) with precomputed BASE_POINT values.
This slows down first getPublicKey() by milliseconds (see Speed section), but allows to speed-up subsequent getPublicKey() calls up to 20x.
You may want to precompute values for your own point.
secp256k1.CURVE.P // Field, 2 ** 256 - 2 ** 32 - 977
secp256k1.CURVE.n // Order, 2 ** 256 - 432420386565659656852420866394968145599
secp256k1.Point.BASE // new secp256k1.Point(Gx, Gy) where
// Gx = 55066263022277343669578718895168534326250603453777594175500187360389116729240n
// Gy = 32670510020758816978083085130507043184471273380659243275938904335757337482424n;
// Elliptic curve point in Affine (x, y) coordinates.
secp256k1.Point {
constructor(x: bigint, y: bigint);
// Supports compressed and non-compressed hex
static fromHex(hex: Uint8Array | string);
static fromPrivateKey(privateKey: Uint8Array | string | number | bigint);
static fromSignature(
msgHash: Hex,
signature: Signature,
recovery: number | bigint
): Point | undefined {
toRawBytes(isCompressed = false): Uint8Array;
toHex(isCompressed = false): string;
equals(other: Point): boolean;
negate(): Point;
add(other: Point): Point;
subtract(other: Point): Point;
// Constant-time scalar multiplication.
multiply(scalar: bigint | Uint8Array): Point;
}
secp256k1.Signature {
constructor(r: bigint, s: bigint);
// DER encoded ECDSA signature
static fromDER(hex: Uint8Array | string);
// R, S 32-byte each
static fromCompact(hex: Uint8Array | string);
assertValidity(): void;
hasHighS(): boolean; // high-S sigs cannot be produced using { canonical: true }
toDERRawBytes(): Uint8Array;
toDERHex(): string;
toCompactRawBytes(): Uint8Array;
toCompactHex(): string;
}
Noble is production-ready.
We're using built-in JS BigInt, which is "unsuitable for use in cryptography" as per official spec. This means that the lib is potentially vulnerable to timing attacks. But, JIT-compiler and Garbage Collector make "constant time" extremely hard to achieve in a scripting language. Which means any other JS library doesn't use constant-time bigints. Including bn.js or anything else. Even statically typed Rust, a language without GC, makes it harder to achieve constant-time for some cases. If your goal is absolute security, don't use any JS lib — including bindings to native ones. Use low-level libraries & languages. Nonetheless we've hardened implementation of koblitz curve multiplication to be algorithmically constant time.
We however consider infrastructure attacks like rogue NPM modules very important; that's why it's crucial to minimize the amount of 3rd-party dependencies & native bindings. If your app uses 500 dependencies, any dep could get hacked and you'll be downloading malware with every npm install. Our goal is to minimize this attack vector.
Benchmarks measured with Apple M1 on MacOS 12.
getPublicKey(utils.randomPrivateKey()) x 6,216 ops/sec @ 160μs/op
sign x 4,789 ops/sec @ 208μs/op
verify x 923 ops/sec @ 1ms/op
recoverPublicKey x 491 ops/sec @ 2ms/op
getSharedSecret aka ecdh x 558 ops/sec @ 1790μs/op
getSharedSecret (precomputed) x 7,105 ops/sec @ 140μs/op
Point.fromHex (decompression) x 12,171 ops/sec @ 82μs/op
schnorr.sign x 409 ops/sec @ 2ms/op
schnorr.verify x 504 ops/sec @ 1ms/op
Compare to other libraries (openssl uses native bindings, not JS):
elliptic#getPublicKey x 1,940 ops/sec
sjcl#getPublicKey x 211 ops/sec
elliptic#sign x 1,808 ops/sec
sjcl#sign x 199 ops/sec
openssl#sign x 4,243 ops/sec
ecdsa#sign x 116 ops/sec
bip-schnorr#sign x 60 ops/sec
elliptic#verify x 812 ops/sec
sjcl#verify x 166 ops/sec
openssl#verify x 4,452 ops/sec
ecdsa#verify x 80 ops/sec
bip-schnorr#verify x 56 ops/sec
elliptic#ecdh x 971 ops/sec
Check out a blog post about this library: Learning fast elliptic-curve cryptography in JS.
npm install to install build dependencies like TypeScriptnpm run compile to compile TypeScript codenpm run test to run jest on test/index.tsSpecial thanks to Roman Koblov, who have helped to improve scalar multiplication speed.
MIT (c) Paul Miller (https://paulmillr.com), see LICENSE file.
FAQs
Fastest 4KB JS implementation of secp256k1 ECDH & ECDSA signatures compliant with RFC6979
The npm package @noble/secp256k1 receives a total of 404,802 weekly downloads. As such, @noble/secp256k1 popularity was classified as popular.
We found that @noble/secp256k1 demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Ensure open-source compliance with Socket’s License Enforcement Beta. Set up your License Policy and secure your software!
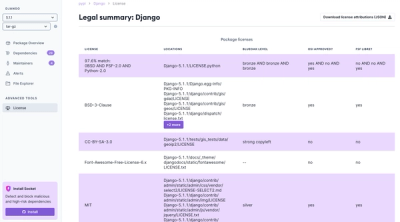
Product
We're launching a new set of license analysis and compliance features for analyzing, managing, and complying with licenses across a range of supported languages and ecosystems.
Product
We're excited to introduce Socket Optimize, a powerful CLI command to secure open source dependencies with tested, optimized package overrides.