
Security News
Maven Central Adds Sigstore Signature Validation
Maven Central now validates Sigstore signatures, making it easier for developers to verify the provenance of Java packages.
constraintjs
Advanced tools

For documentation or the full ConstraintJS API, visit cjs.from.so/.
If you'd rather build from this repository, you must install node.js and Grunt. Then, from inside the constraintjs source directory, run:
npm install .
grunt
The CJS Library will appear in the build/ directory.
Make changes to the files in src/ instead of build/. After you change a file, be sure to run grunt to re-build the files in build/. By default, the sourcemap generated for build/cjs.min.js links to the build/cjs.js file. To build a sourcemap that links back to the original src/ files (significantly more useful for development), change grunt in the instructions above to grunt dev:
npm install .
grunt dev
FAQs
Constraint library for JavaScript
The npm package constraintjs receives a total of 0 weekly downloads. As such, constraintjs popularity was classified as not popular.
We found that constraintjs demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

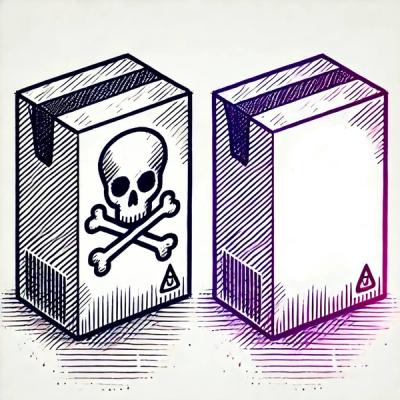
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Maven Central now validates Sigstore signatures, making it easier for developers to verify the provenance of Java packages.

Security News
CISOs are racing to adopt AI for cybersecurity, but hurdles in budgets and governance may leave some falling behind in the fight against cyber threats.
Research
Security News
Socket researchers uncovered a backdoored typosquat of BoltDB in the Go ecosystem, exploiting Go Module Proxy caching to persist undetected for years.