
Product
Introducing License Enforcement in Socket
Ensure open-source compliance with Socket’s License Enforcement Beta. Set up your License Policy and secure your software!
The jwa npm package is a JavaScript implementation of JSON Web Algorithms (JWA) as specified in RFC 7518. It provides functionality to perform cryptographic operations such as signing and verifying signatures using various algorithms.
Signing
This feature allows you to create a signature for a given payload using a specified algorithm and secret. The 'HS256' algorithm is used in this example to sign the 'Hello, world!' payload.
"use strict";\nconst jwa = require('jwa');\nconst algorithm = 'HS256';\nconst hmac = jwa(algorithm);\nconst secret = 'mysecret';\nconst payload = 'Hello, world!';\nconst signature = hmac.sign(payload, secret);\nconsole.log('Signature:', signature);Verifying Signatures
This feature allows you to verify a signature for a given payload using the same algorithm and secret that were used to sign the payload. It returns a boolean indicating whether the signature is valid.
"use strict";\nconst jwa = require('jwa');\nconst algorithm = 'HS256';\nconst hmac = jwa(algorithm);\nconst secret = 'mysecret';\nconst payload = 'Hello, world!';\nconst signature = 'signatureFromSigning';\nconst isValid = hmac.verify(payload, signature, secret);\nconsole.log('Is signature valid?', isValid);jsonwebtoken is a popular npm package that implements JSON Web Tokens (JWT). It can be used to create and verify tokens that are signed with a secret or a public/private key. Unlike jwa, which focuses on the algorithms for signing and verifying, jsonwebtoken provides a higher-level API for handling JWTs, including payload encoding and decoding.
node-jose is a library for JavaScript Object Signing and Encryption (JOSE). It provides a comprehensive suite of tools for working with JOSE standards, including JWA, JSON Web Key (JWK), JSON Web Signature (JWS), and JSON Web Encryption (JWE). Compared to jwa, node-jose offers a broader set of functionalities for handling encryption and key management in addition to signing and verification.
jws is a simple library to create and verify JSON Web Signatures (JWS). It is similar to jwa in that it focuses on the signing and verification of messages but provides a slightly different API and additional features for handling JWS objects directly.

A JSON Web Algorithms implementation focusing (exclusively, at this point) on the algorithms necessary for JSON Web Signatures.
This library supports all of the required, recommended and optional cryptographic algorithms for JWS:
| alg Parameter Value | Digital Signature or MAC Algorithm |
|---|---|
| HS256 | HMAC using SHA-256 hash algorithm |
| HS384 | HMAC using SHA-384 hash algorithm |
| HS512 | HMAC using SHA-512 hash algorithm |
| RS256 | RSASSA using SHA-256 hash algorithm |
| RS384 | RSASSA using SHA-384 hash algorithm |
| RS512 | RSASSA using SHA-512 hash algorithm |
| ES256 | ECDSA using P-256 curve and SHA-256 hash algorithm |
| ES384 | ECDSA using P-384 curve and SHA-384 hash algorithm |
| ES512 | ECDSA using P-521 curve and SHA-512 hash algorithm |
| none | No digital signature or MAC value included |
In order to run the tests, a recent version of OpenSSL is required. The version that comes with OS X (OpenSSL 0.9.8r 8 Feb 2011) is not recent enough, as it does not fully support ECDSA keys. You'll need to use a version > 1.0.0; I tested with OpenSSL 1.0.1c 10 May 2012.
To run the tests, do
$ npm test
This will generate a bunch of keypairs to use in testing. If you want to
generate new keypairs, do make clean before running npm test again.
To test interoperability, some tests spawn openssl dgst -sha[bits] -sign [keyfile]
to generate the signature and verify it using jwa#verify.
Creates a new jwa object with sign and verify methods for the
algorithm. Valid values for algorithm can be found in the table above
('HS256', 'HS384', etc) and are case-insensitive. Passing an invalid
algorithm value will throw a TypeError.
Sign some input with either a secret for HMAC algorithms, or a private key for RSA and ECDSA algorithms.
If input is not already a string or buffer, JSON.stringify will be
called on it to attempt to coerce it.
For the HMAC algorithm, secretOrPrivateKey should be a string or a
buffer. For ECDSA and RSA, the value should be a string represented a
PEM encoded private key.
Output base64url formatted. This is for convenience as JWS expects the signature in this format. If your application needs the output in a different format, please open an issue. In the meantime, you can use brianloveswords/base64url to decode the signature.
Verify a signature. Returns true or false.
signature should be a base64url encoded string.
For the HMAC algorithm, secretOrPublicKey should be a string or a
buffer. For ECDSA and RSA, the value should be a string represented a
PEM encoded public key.
HMAC
const jwa = require('jwa');
const hmac = jwa('hs256');
const input = 'super important stuff';
const secret = 'shhhhhh';
const signature = hmac.sign(input, secret);
hmac.verify(input, signature, secret) // === true
hmac.verify(input, signature, 'trickery!') // === false
With keys
const fs = require('fs');
const jwa = require('jwa');
const privateKey = fs.readFileSync(__dirname + '/ecdsa-p521-private.pem');
const publicKey = fs.readFileSync(__dirname + '/ecdsa-p521-public.pem');
const ecdsa = jwa('es512');
const input = 'very important stuff';
const signature = ecdsa.sign(input, privateKey);
ecdsa.verify(input, signature, publicKey) // === true
MIT
Copyright (c) 2013 Brian J. Brennan
Permission is hereby granted, free of charge, to any person obtaining a copy
of this software and associated documentation files (the "Software"), to deal in
the Software without restriction, including without limitation the rights to use,
copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the
Software, and to permit persons to whom the Software is furnished to do so,
subject to the following conditions:
The above copyright notice and this permission notice shall be included in all
copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED,
INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR
PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE
FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE,
ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.
FAQs
JWA implementation (supports all JWS algorithms)
The npm package jwa receives a total of 20,345,028 weekly downloads. As such, jwa popularity was classified as popular.
We found that jwa demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 3 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Ensure open-source compliance with Socket’s License Enforcement Beta. Set up your License Policy and secure your software!
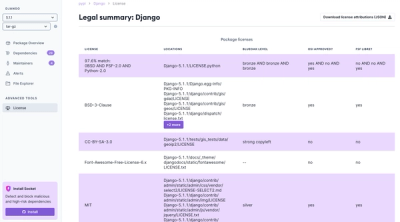
Product
We're launching a new set of license analysis and compliance features for analyzing, managing, and complying with licenses across a range of supported languages and ecosystems.
Product
We're excited to introduce Socket Optimize, a powerful CLI command to secure open source dependencies with tested, optimized package overrides.