
Security News
PyPI’s New Archival Feature Closes a Major Security Gap
PyPI now allows maintainers to archive projects, improving security and helping users make informed decisions about their dependencies.
storj-service-storage-models
Advanced tools
Common storage models for various Storj services
npm install storj-service-storage-models --save
var Storage = require('storj-service-storage-models');
var db = new Storage(
'mongodb://127.0.0.1:27017/storj-bridge-database-name',
{
auth: {
user: 'myuser',
pass: 'mypassword'
},
mongos: {
ssl: true
}
},
{
logger: myAwesomeLogger
});
db.models.User.findOne({ email: 'gordon@storj.io' }, function(err, user) {
if (err) {
console.error(err.message);
} else {
console.info(user);
}
});
You'll have to set Coinpayments environment variables CP_PUBLIC_KEY and CP_SECRET_KEY in order to get coinpayments client working with the payment processor adapter.
If using billing functionality, be sure to include your own .env file with necessary environment variables.
FAQs
common storage models for various storj services
The npm package storj-service-storage-models receives a total of 99 weekly downloads. As such, storj-service-storage-models popularity was classified as not popular.
We found that storj-service-storage-models demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 7 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
PyPI now allows maintainers to archive projects, improving security and helping users make informed decisions about their dependencies.

Research
Security News
Malicious npm package postcss-optimizer delivers BeaverTail malware, targeting developer systems; similarities to past campaigns suggest a North Korean connection.
Security News
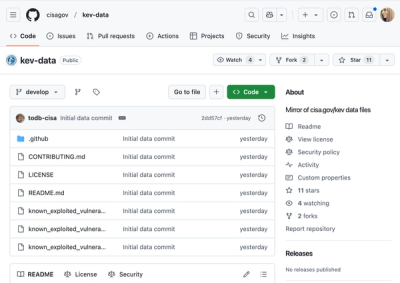
CISA's KEV data is now on GitHub, offering easier access, API integration, commit history tracking, and automated updates for security teams and researchers.