
Security News
The Push to Ban Ransom Payments Is Gaining Momentum
Ransomware costs victims an estimated $30 billion per year and has gotten so out of control that global support for banning payments is gaining momentum.
twitter-lite
Advanced tools
Readme
A tiny, full-featured, modern client / server library for the Twitter API.
We have built this library because existing ones have not been recently maintained, or depend on outdated libraries.
yarn add twitter-lite
npm install twitter-lite
Twitter has two different authentication options:
User authentication requires:
consumer_keyconsumer_secretaccess_token_keyaccess_token_secretApp authentication requires:
bearer_tokenApp authentication is a simple header behind the scenes:
headers: {
Authorization: `Bearer ${bearer_token}`;
}
You can get the bearer token by calling .getBearerToken().
const client = new Twitter({
subdomain: "api",
consumer_key: "abc", // from Twitter.
consumer_secret: "def", // from Twitter.
access_token_key: "uvw", // from your User (oauth_token)
access_token_secret: "xyz" // from your User (oauth_token_secret)
});
client
.get("account/verify_credentials")
.then(results => {
console.log("results", results);
})
.catch(console.error);
const user = new Twitter({
consumer_key: "abc",
consumer_secret: "def",
});
const response = await user.getBearerToken();
const app = new Twitter({
bearer_token: response.access_token
});
According to the docs this helps you get access token from your users.
const client = new Twitter({
consumer_key: "xyz",
consumer_secret: "xyz"
});
client
.getRequestToken("http://callbackurl.com")
.then(res =>
console.log({
reqTkn: res.oauth_token,
reqTknSecret: res.oauth_token_secret
})
)
.catch(console.error);
Then you redirect your user to https://api.twitter.com/oauth/authenticate?oauth_token=xyz123abc, and once you get the verifier and the token, you pass them on to the next stage of the authentication.
const client = new Twitter({
consumer_key: "xyz",
consumer_secret: "xyz"
});
client
.getAccessToken({
key: requestToken,
secret: requestTokenSecret,
verifier: oauthVerifier
})
.then(res =>
console.log({
accTkn: res.oauth_token,
accTknSecret: res.oauth_token_secret,
userId: res.user_id,
screenName: res.screen_name
})
)
.catch(console.error);
And this will return you your access_token and access_token_secret.
To learn more about the streaming API visit the Twitter Docs. The streaming API works only in Node.
const client = new Twitter({
consumer_key: "xyz" // from Twitter.
consumer_secret: "xyz" // from Twitter.
access_token_key: "abc" // from your User (oauth_token)
access_token_secret: "abc" // from your User (oauth_token_secret)
});
const parameters = {
track: "#bitcoin,#litecoin,#monero", // #bitcoin, #litecoin, #monero
follow: "422297024,873788249839370240", // @OrchardAI, @tylerbuchea
locations: "-122.75,36.8,-121.75,37.8", // Bounding box - San Francisco
};
client.stream("statuses/filter", parameters)
.on("start", response => console.log("start"))
.on("data", data => console.log("data", data.text))
.on("ping", () => console.log("ping"))
.on("error", error => console.log("error", error))
.on("end", response => console.log("end"));
// to stop the stream:
client.stream.destroy(); // emits "end" and "error" event
const client = new Twitter({
consumer_key: "xyz",
consumer_secret: "xyz",
access_token_key: "abc",
access_token_secret: "abc"
});
const rateLimits = await app.get("statuses/show", {
id: "1016078154497048576",
});
Use the .post method for actions that change state, as documented in the Twitter API. For example, to follow a user:
const client = new Twitter({
consumer_key: "xyz",
consumer_secret: "xyz",
access_token_key: "abc",
access_token_secret: "abc"
});
await client.post("friendships/create", null, {
screen_name: "dandv"
});
Note: for now, make sure to pass a null body to .post. This is subject to change in a future version of the library.
See the app authenticatio example.
See the OAuth example.
See the OAuth example.
API errors are returned as an array of errors under the errors key of the response object. Make sure to check for the presence of this field, in addition to any try/catch blocks you may have.
Twitter uses numeric IDs that in practice can be up to 18 characters long. Due to rounding errors, it's unsafe to use numeric IDs in JavaScript. Always set stringify_ids: true when possible, so that Twitter will return strings instead of numbers, and rely on the id_str field, rather than on the id field.
With the library nearing v1.0, contributions are welcome! Areas especially in need of help involve multimedia (see #33 for example), adding tests (see these for reference), and getting v1.0 out the door.
yarn/npm installTWITTER_CONSUMER_KEY=...
TWITTER_CONSUMER_SECRET=...
ACCESS_TOKEN=...
ACCESS_TOKEN_SECRET=...
yarn/npm test and make sure all tests passit() call to it.skip(), but remember to revert that change before committing. This will prevent your account from being flagged as abusing the API to send too many DMs.npm run precommit for linting with prettiergit push and submit your PR!Authors:
Over the years, thanks to:
FAQs
Tiny, full-featured client/server REST/stream library for the Twitter API
We found that twitter-lite demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 2 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Ransomware costs victims an estimated $30 billion per year and has gotten so out of control that global support for banning payments is gaining momentum.
Application Security
New SEC disclosure rules aim to enforce timely cyber incident reporting, but fear of job loss and inadequate resources lead to significant underreporting.
Security News
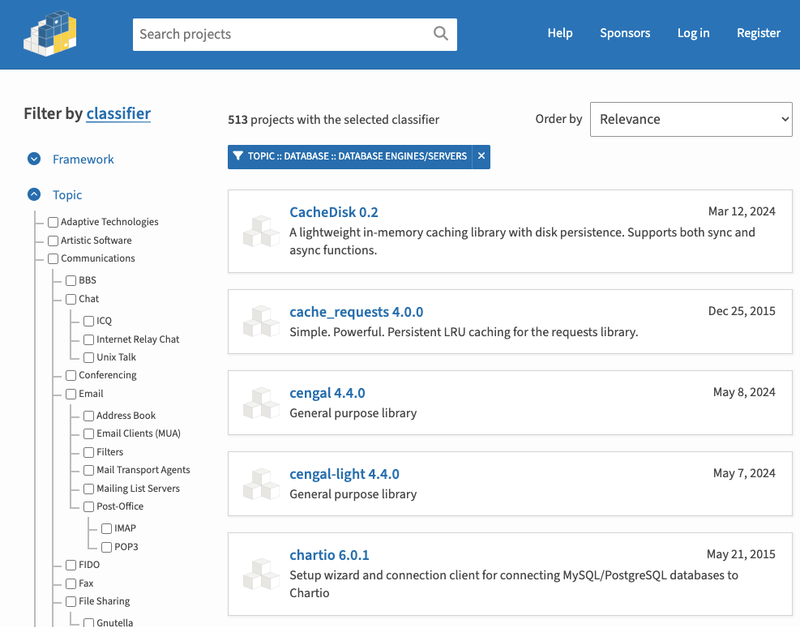
The Python Software Foundation has secured a 5-year sponsorship from Fastly that supports PSF's activities and events, most notably the security and reliability of the Python Package Index (PyPI).