
Security News
Crates.io Users Targeted by Phishing Emails
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
Description: My custom format algorithm with loosy RAM allocation and terribly huge time and space complexity that bloats and debloats string and string-like types.
Using bloat/debloat for basic stage format:
# Importing the package
from bloatier import bloatier
string_ = "This is a string" # Our string to be bloated
bloated_string = bloatier.bloat(string_) # Bloated string
# Print the bloated string
print("Bloated String:\n", bloated_string)
# Print the debloated string
print("Debloated String\n", bloatier.debloat(bloated_string))
Note: You can also use bloats/debloats for multi-stage format. (if you have enough RAM :>)
The string being used by the algorithm and the outputs are all stored in a dictionary "obtain" and can be acquired by using the acquired function.
There is a main bloatier class and 5 local functions related to the main class.
FAQs
Basic String Bloater/Debloater Algorithm.
We found that bloatier demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

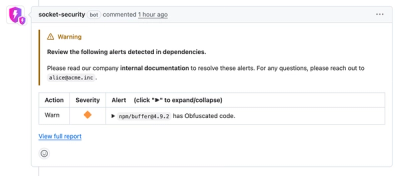
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
Product
Socket now lets you customize pull request alert headers, helping security teams share clear guidance right in PRs to speed reviews and reduce back-and-forth.

Product
Socket's Rust support is moving to Beta: all users can scan Cargo projects and generate SBOMs, including Cargo.toml-only crates, with Rust-aware supply chain checks.