
Security News
Crates.io Users Targeted by Phishing Emails
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
.. image:: https://circleci.com/gh/ICIJ/solr2es.png?style=shield&circle-token=846c844f540fb3746b80b8f12656ddde665b5037 :alt: Circle CI :target: https://circleci.com/gh/ICIJ/solr2es
Migration script from solr to elasticsearch via a queue, that could be either redis or postgresql.
Here are the option to use as a command line :
.. image:: examples/solr2es_process.png :alt: solr2es process :align: center
translation_map
.. image:: examples/migration.jpg :alt: migration map :align: center
The purpose of a translation_map is to create a mapping between the fields coming from the queue (either Redis or Postgresql) to the ones inserted to Elasticsearch.
If a field from the queue doesn't exist in the translation_map, it will be inserted as it is into Elasticsearch.
Use the property name to rename a field in Elasticsearch :
::
{"queue_name": {"name": "elasticsearch_name"}}
3. Use the property default if you want to set a default value into a field in Elasticsearch.
If the field exists into the queue and has a value, it won't be changed by the translation_map. Otherwise a field queue_name willl be added to Elasticsearch with value john doe.
::
{"queue_name": {"default": "john doe"}}
4. Use the property name with some . in it, to create a nested field in Elasticsearch.
If the queue record has a field nested_a_b, the Elasticsearch record will get a field nested, that will have a nested field a, that will have a nested field b that will get the content of nested_a_b.
::
{"nested_a_b": {"name": "nested.a.b"}}
5. Use the property name with some regex groups capture to rename a bulk of queue fields in Elasticsearch by adding [regexp] at the beginning of the field.
This will rename all the fields prefixed by queue_ into elasticsearch_.
::
{"[regexp]queue_(.*)": {"name": "elasticsearch_\\1"}}
6. Use the property ignore at true to ignore some fields from the queue to Elasticsearch.
::
{"ignored_field": {"ignore": true}}
7. Use the property routing_field set to true to use one field for routing in elasticsearch. An exception will be raised if several fields are set to true.
::
{"my_root_doc": {"routing_field": true}}
8. Use the property multivalued set to false to ignore multi valued array field. Get the first value instead. By default the array is copied.
::
{"my_array": {"multivalued": false}}
execution
::
solr2es --postgresqldsn 'dbname=solr2es user=test password=test host=localhost' --solrhost 127.0.0.1 --core test_core --solrid solr_id -d -a
2. Execute a resume from Postgresql into Elasticsearch specifying the Postgresql DSN, the Elasticsearch index, the Elasticsearch mapping, the Elasticsearch settings and the translation map
::
solr2es --postgresqldsn 'dbname=solr2es user=test password=test host=localhost' --index es-index --translationmap @examples/translation-map.json --esmapping @examples/datashare_index_mappings.json --essetting @examples/datashare_index_settings.json -r -a
To build and run tests you can make :
::
virtualenv --python=python3.6 venv
source venv/bin/activate
python setup.py develop
python setup.py test
To release :
::
python setup.py sdist bdist_egg upload
Some features are not implemented yet :
FAQs
Python solr/elasticsearch migration script
We found that solr2es demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

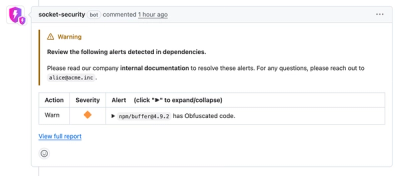
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
Product
Socket now lets you customize pull request alert headers, helping security teams share clear guidance right in PRs to speed reviews and reduce back-and-forth.

Product
Socket's Rust support is moving to Beta: all users can scan Cargo projects and generate SBOMs, including Cargo.toml-only crates, with Rust-aware supply chain checks.