
Security News
38% of CISOs Fear They’re Not Moving Fast Enough on AI
CISOs are racing to adopt AI for cybersecurity, but hurdles in budgets and governance may leave some falling behind in the fight against cyber threats.
@amaui/hash-table
Advanced tools
Hash table
Very simple code Modern code Junior friendly Typescript Made with :yellow_heart:
// yarn
yarn add @amaui/hash-table
// npm
npm install @amaui/hash-table
import AmauiHashTable from '@amaui/hash-table';
// Make a new hash table instance
const amauiHashTable = new AmauiHashTable();
// Add values
amauiHashTable.set('a', 14).set('a1', 114);
amauiHashTable.get('a');
// 14
amauiHashTable.get('a14');
// undefined
// Remove
amauiHashTable.remove('a');
// true
amauiHashTable.get('a');
// undefined
Install
yarn
Test
yarn test
Build
yarn build
Might be soon...
FAQs
Hash table
We found that @amaui/hash-table demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
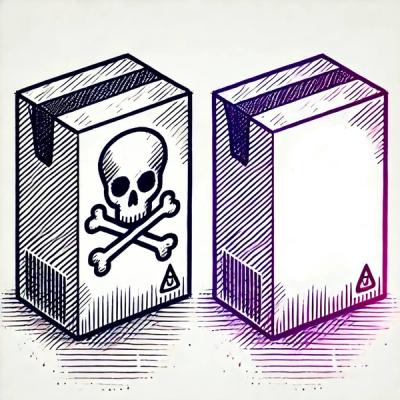
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
CISOs are racing to adopt AI for cybersecurity, but hurdles in budgets and governance may leave some falling behind in the fight against cyber threats.
Research
Security News
Socket researchers uncovered a backdoored typosquat of BoltDB in the Go ecosystem, exploiting Go Module Proxy caching to persist undetected for years.

Security News
Company News
Socket is joining TC54 to help develop standards for software supply chain security, contributing to the evolution of SBOMs, CycloneDX, and Package URL specifications.