Security News
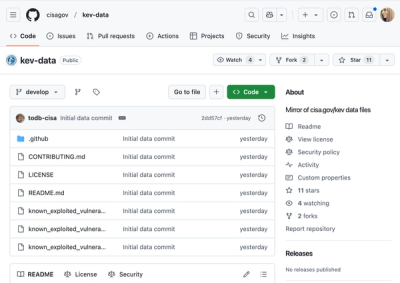
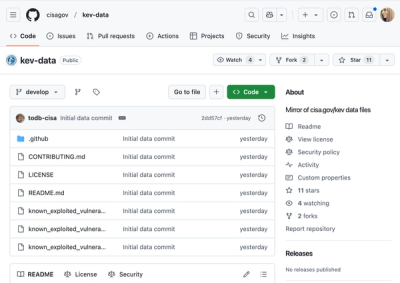
CISA Brings KEV Data to GitHub
CISA's KEV data is now on GitHub, offering easier access, API integration, commit history tracking, and automated updates for security teams and researchers.
@aws-cdk/aws-dax
Advanced tools
All classes with the
Cfnprefix in this module (CFN Resources) are always stable and safe to use.
This module is part of the AWS Cloud Development Kit project.
import * as dax from '@aws-cdk/aws-dax';
There are no hand-written (L2) constructs for this service yet. However, you can still use the automatically generated L1 constructs, and use this service exactly as you would using CloudFormation directly.
For more information on the resources and properties available for this service, see the CloudFormation documentation for AWS::DAX.
(Read the CDK Contributing Guide if you are interested in contributing to this construct library.)
1.152.0 (2022-04-06)
cdk import (#17666) (4f12209)Fn.select incorrectly short-circuits complex expressions (#19680) (7f26fad)FAQs
The CDK Construct Library for AWS::DAX
The npm package @aws-cdk/aws-dax receives a total of 479 weekly downloads. As such, @aws-cdk/aws-dax popularity was classified as not popular.
We found that @aws-cdk/aws-dax demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 4 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Security News
CISA's KEV data is now on GitHub, offering easier access, API integration, commit history tracking, and automated updates for security teams and researchers.

Security News
Opengrep forks Semgrep to preserve open source SAST in response to controversial licensing changes.

Security News
Critics call the Node.js EOL CVE a misuse of the system, sparking debate over CVE standards and the growing noise in vulnerability databases.