Security News
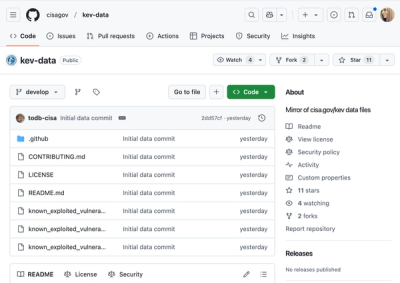
CISA Brings KEV Data to GitHub
CISA's KEV data is now on GitHub, offering easier access, API integration, commit history tracking, and automated updates for security teams and researchers.
@conveyal/analysis-ui
Advanced tools
Conveyal's tools for editing land-use/transportation scenarios.
The Scenario Editor needs an Analyst backend running to point at. By default it expects it to be running at http://localhost:7070.
Copy the /configurations/default/env.yml.tmp to /configurations/default/env.yml and add your Auth0 credentials. If you're running locally (for testing or development) you don't need to use Auth0. Just comment out the Auth0 lines and it should work. You'll also need some tile URLs for Leaflet. The default Mapbox URLs require an access key. If you're at Conveyal, you can grab these keys and other settings from our se-configurations repository on Github.
First make sure you're running the latest Node and NPM. For example, on a Mac using Homebrew:
$ brew update
$ brew upgrade node
Then build and start the scenario editor:
$ npm install && npm start
FAQs
Conveyal's tool for editing land use/transportation scenarios.
We found that @conveyal/analysis-ui demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 5 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
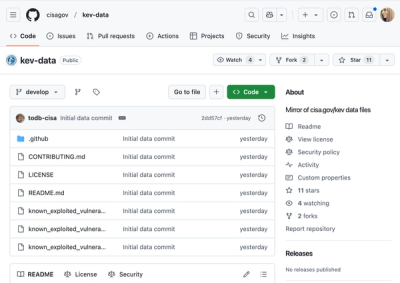
Security News
CISA's KEV data is now on GitHub, offering easier access, API integration, commit history tracking, and automated updates for security teams and researchers.

Security News
Opengrep forks Semgrep to preserve open source SAST in response to controversial licensing changes.

Security News
Critics call the Node.js EOL CVE a misuse of the system, sparking debate over CVE standards and the growing noise in vulnerability databases.