Security News
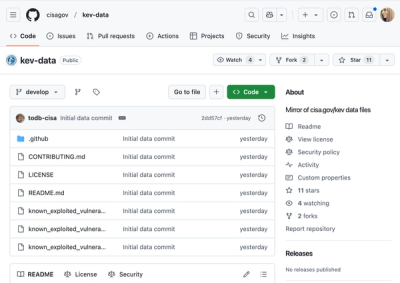
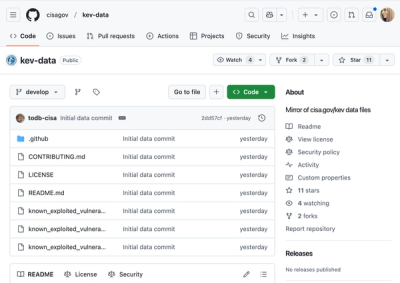
CISA Brings KEV Data to GitHub
CISA's KEV data is now on GitHub, offering easier access, API integration, commit history tracking, and automated updates for security teams and researchers.
@purple/phoenix-components
Advanced tools
⚠️Please note this is an early stage project and the components may change at any time.
⚠️Please note this is an early stage project and the components may change at any time.
Our aim is to build a simple React component library using styled components and typescript.
3rd party libraries
Phoenix components takes advantage of some 3rd party libraries and provides consistent styling for them.
react-select for the Selectbox componentreact-dropzone for the FileUpload componentDocumentation
Install
npm i @purple/phoenix-components
or
yarn add @purple/phoenix-components
Import components
import { Input } from "@purple/phoenix-components"
FAQs
[](https://percy.io/Purple-Technology/phoenix-components)
The npm package @purple/phoenix-components receives a total of 271 weekly downloads. As such, @purple/phoenix-components popularity was classified as not popular.
We found that @purple/phoenix-components demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 0 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Security News
CISA's KEV data is now on GitHub, offering easier access, API integration, commit history tracking, and automated updates for security teams and researchers.

Security News
Opengrep forks Semgrep to preserve open source SAST in response to controversial licensing changes.

Security News
Critics call the Node.js EOL CVE a misuse of the system, sparking debate over CVE standards and the growing noise in vulnerability databases.