
Security News
pnpm 10.0.0 Blocks Lifecycle Scripts by Default
pnpm 10 blocks lifecycle scripts by default to improve security, addressing supply chain attack risks but sparking debate over compatibility and workflow changes.
@subasshrestha/merkletreejs
Advanced tools

Construct Merkle Trees and verify proofs in JavaScript.
From NPM:
npm install merkletreejs
Available on jsDelivr CDN:
<script src="https://cdn.jsdelivr.net/npm/merkletreejs@latest/merkletree.js"></script>
https://lab.miguelmota.com/merkletreejs
Construct tree, generate proof, and verify proof:
const { MerkleTree } = require('merkletreejs')
const SHA256 = require('crypto-js/sha256')
const leaves = ['a', 'b', 'c'].map(x => SHA256(x))
const tree = new MerkleTree(leaves, SHA256)
const root = tree.getRoot().toString('hex')
const leaf = SHA256('a')
const proof = tree.getProof(leaf)
console.log(tree.verify(proof, leaf, root)) // true
const badLeaves = ['a', 'x', 'c'].map(x => SHA256(x))
const badTree = new MerkleTree(badLeaves, SHA256)
const badLeaf = SHA256('x')
const badProof = tree.getProof(badLeaf)
console.log(tree.verify(badProof, leaf, root)) // false
Print tree to console:
console.log(tree.toString())
Output:
└─ 7075152d03a5cd92104887b476862778ec0c87be5c2fa1c0a90f87c49fad6eff
├─ e5a01fee14e0ed5c48714f22180f25ad8365b53f9779f79dc4a3d7e93963f94a
│ ├─ ca978112ca1bbdcafac231b39a23dc4da786eff8147c4e72b9807785afee48bb
│ └─ 3e23e8160039594a33894f6564e1b1348bbd7a0088d42c4acb73eeaed59c009d
└─ 2e7d2c03a9507ae265ecf5b5356885a53393a2029d241394997265a1a25aefc6
└─ 2e7d2c03a9507ae265ecf5b5356885a53393a2029d241394997265a1a25aefc6
▾ Visualization of Merkle Tree

▾ Visualization of Merkle Tree Proof

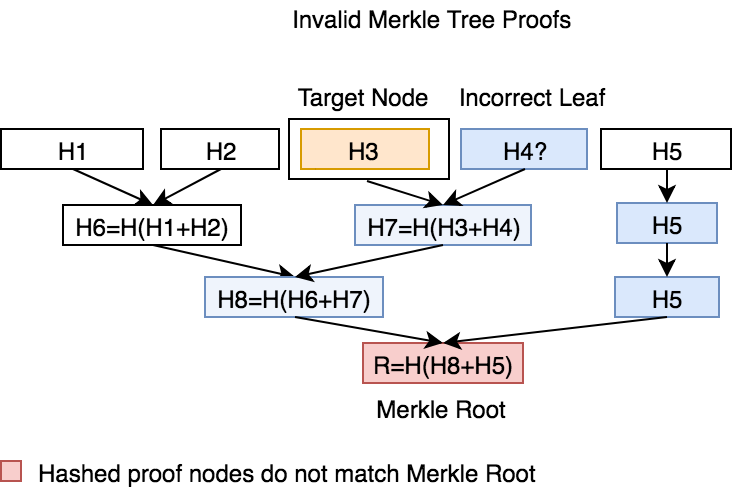
▾ Visualization of Invalid Merkle Tree Proofs
▾ Visualization of Bitcoin Merkle Tree

See documentation (under docs/)
npm test
Q: How do you verify merkle proofs in Solidity?
Q: How do you verify merkle multiproofs in Solidity?
Q: Is there a CLI version?
As is, this implemenation is vulnerable to a second pre-image attack. Use a difference hashing function for leaves and nodes, so that H(x) != H'(x).
Also, as is, this implementation is vulnerable to a forgery attack for an unbalanced tree, where the last leaf node can be duplicated to create an artificial balanced tree, resulting in the same Merkle root hash. Do not accept unbalanced tree to prevent this.
More info here.
Bitcoin mining the hard way: the algorithms, protocols, and bytes
Why aren't Solidity sha3 hashes not matching what other sha3 libraries produce?
What is the purpose of using different hash functions for the leaves and internals of a hash tree?
Pull requests are welcome!
For contributions please create a new branch and submit a pull request for review.
Many thanks to all the contributors that made this library better.
FAQs
Construct Merkle Trees and verify proofs
We found that @subasshrestha/merkletreejs demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
pnpm 10 blocks lifecycle scripts by default to improve security, addressing supply chain attack risks but sparking debate over compatibility and workflow changes.

Product
Socket now supports uv.lock files to ensure consistent, secure dependency resolution for Python projects and enhance supply chain security.

Research
Security News
Socket researchers have discovered multiple malicious npm packages targeting Solana private keys, abusing Gmail to exfiltrate the data and drain Solana wallets.