Security News
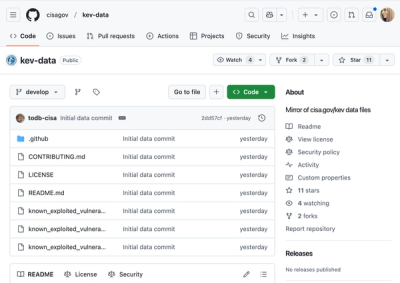
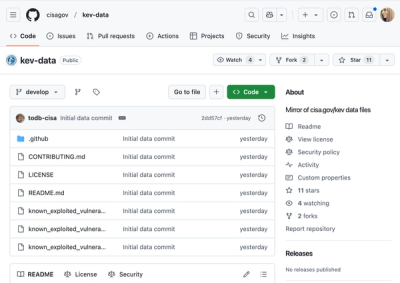
CISA Brings KEV Data to GitHub
CISA's KEV data is now on GitHub, offering easier access, API integration, commit history tracking, and automated updates for security teams and researchers.
MIT-licensed, client-side, JavaScript framework that makes building rich web applications easy.
WARNING: This npm package is for the CanJS client-side MV* libraries. It was formerly the node-can project which has been moved to socketcan. A HUGE thanks to Sebastian Haas for letting us use the
canname!
NOTE: The
canjsNPM package name is deprecated. Usecaninstead.
CanJS is a collection of the following client-side JavaScript architectural libraries:
The best, most hardened and generally useful libraries in CanJS.
Utility libraries that power the core and ecosystem collections.
Useful libraries that extend or add important features to the core collection.
Former libraries that we still accept patches for, but are not under active development.
Before you make an issue, please read our Contributing guide.
You can find the core team on Slack.
See Releases.
FAQs
MIT-licensed, client-side, JavaScript framework that makes building rich web applications easy.
We found that can demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 11 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Security News
CISA's KEV data is now on GitHub, offering easier access, API integration, commit history tracking, and automated updates for security teams and researchers.

Security News
Opengrep forks Semgrep to preserve open source SAST in response to controversial licensing changes.

Security News
Critics call the Node.js EOL CVE a misuse of the system, sparking debate over CVE standards and the growing noise in vulnerability databases.