
Research
Security News
Malicious npm Packages Inject SSH Backdoors via Typosquatted Libraries
Socket’s threat research team has detected six malicious npm packages typosquatting popular libraries to insert SSH backdoors.
px-tag-list
Advanced tools
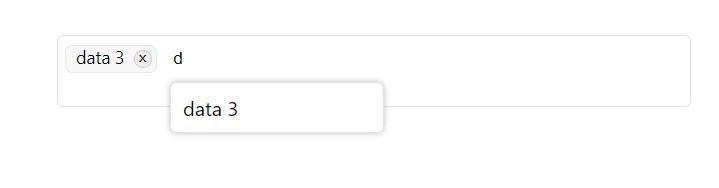
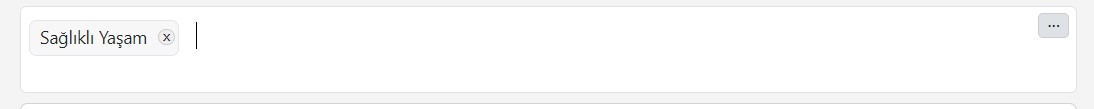
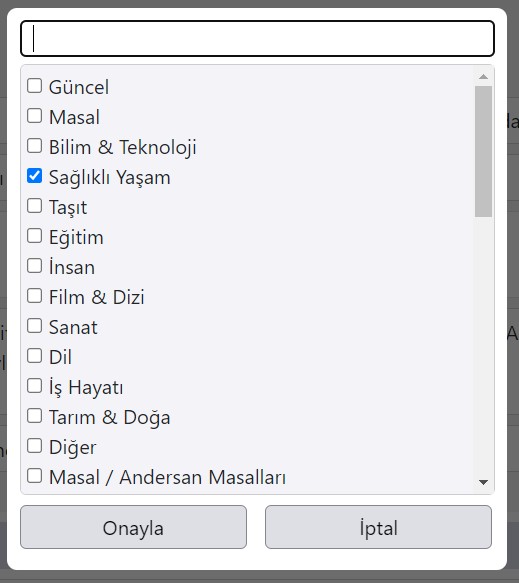
It is used to add a label (tag). Dynamic data can be retrieved with Ajax, Javascript data can be used or data-independent user input tags can be added. With the modal feature, ready data can be searched on a larger screen. Autocomplate is used when writin
npm i jquery
npm i px-tag-list
@import "~px-tag-list/px-tag-list.css";
require('px-tag-list');
<div id="objectid"></div>
$("#objectid").pxtaglist({
name: "object_name",
/use ajaxpage or data/
ajaxpage: "api/user/content/category/list",
data: [{ id: '1', text: 'Data 1' }, { id: '2', text: 'Data 2' }, { id: '3', text: 'data 3' }],
addnew: false,
modal: true,
modal_approve_text: "Approve",
modal_cancel_text: "Cancel",
minheight: 70,
style: "",
class: "",
callback: function (e) {
console.log(e);
}
});
PHP POST CODE EXAMPLE:
$data = $_POST["object_name"];
$resultdata = json_decode($data);
It is used to add a label (tag). Dynamic data can be retrieved with Ajax, Javascript data can be used or data-independent user input tags can be added. With the modal feature, ready data can be searched on a larger screen. Autocomplate is used when writing tags. it doesn't add the previously added tag again!
FAQs
It is used to add a label (tag). Dynamic data can be retrieved with Ajax, Javascript data can be used or data-independent user input tags can be added. With the modal feature, ready data can be searched on a larger screen. Autocomplate is used when writin
The npm package px-tag-list receives a total of 0 weekly downloads. As such, px-tag-list popularity was classified as not popular.
We found that px-tag-list demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Research
Security News
Socket’s threat research team has detected six malicious npm packages typosquatting popular libraries to insert SSH backdoors.

Security News
MITRE's 2024 CWE Top 25 highlights critical software vulnerabilities like XSS, SQL Injection, and CSRF, reflecting shifts due to a refined ranking methodology.

Security News
In this segment of the Risky Business podcast, Feross Aboukhadijeh and Patrick Gray discuss the challenges of tracking malware discovered in open source softare.