
Security News
Research
Data Theft Repackaged: A Case Study in Malicious Wrapper Packages on npm
The Socket Research Team breaks down a malicious wrapper package that uses obfuscation to harvest credentials and exfiltrate sensitive data.
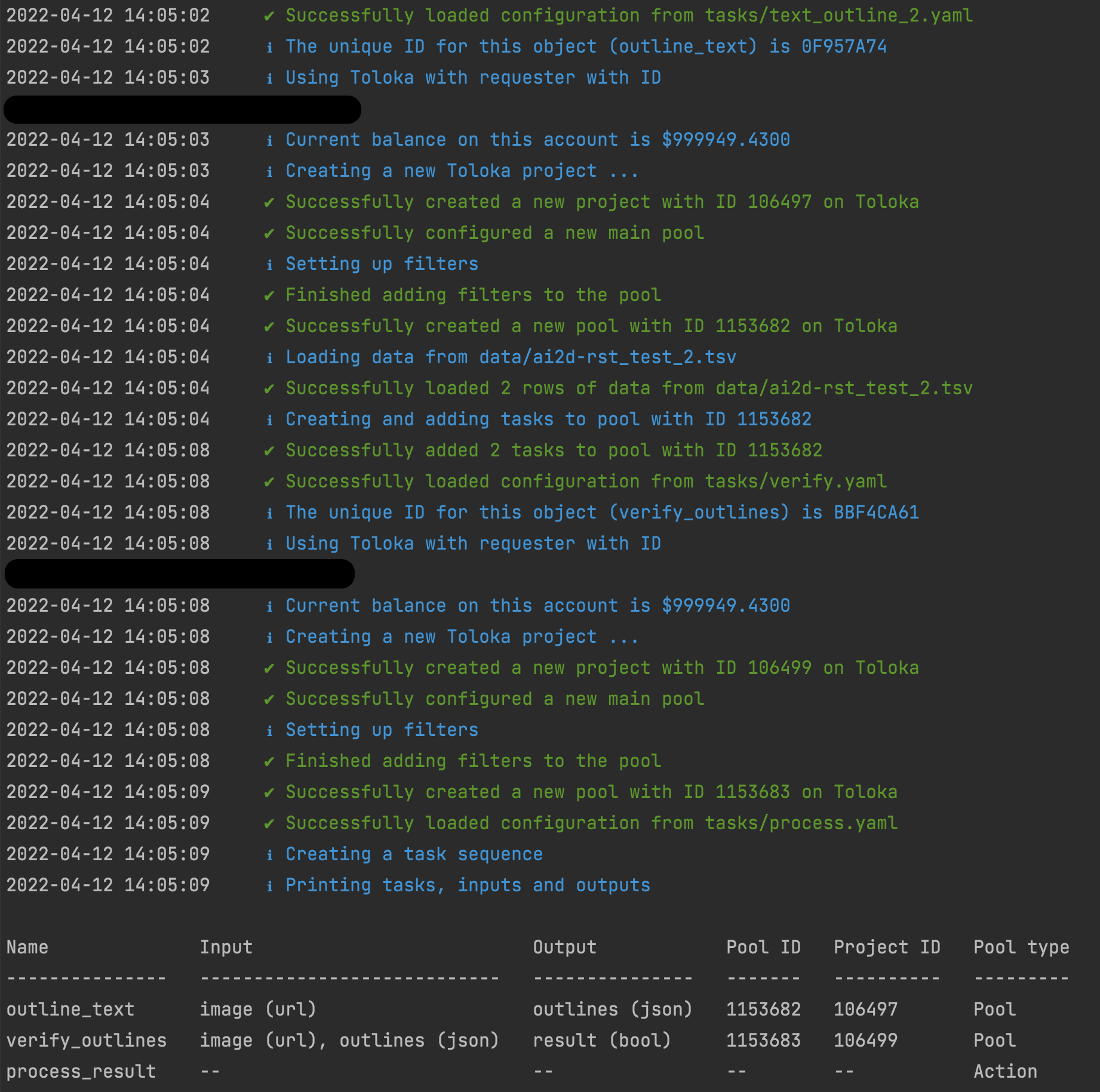
𝚊𝚋𝚞𝚕𝚊𝚏𝚒𝚊 is a tool for creating and deploying tasks on the the Toloka crowdsourcing platform.
The tool allows you to create crowdsourcing tasks using pre-defined task interfaces and to configure their settings using YAML files.
For a description of the tool and the motivation for its development, see this publication.
Please cite the following publication if you use the tool in your research.
Tuomo Hiippala, Helmiina Hotti, and Rosa Suviranta. 2022. Developing a tool for fair and reproducible use of paid crowdsourcing in the digital humanities. In Proceedings of the 6th Joint SIGHUM Workshop on Computational Linguistics for Cultural Heritage, Social Sciences, Humanities and Literature, pages 7–12, Gyeongju, Republic of Korea. International Conference on Computational Linguistics.
For convenience, you can use the BibTeX entry below.
@inproceedings{hiippala-etal-2022-developing,
title = "Developing a tool for fair and reproducible use of paid crowdsourcing in the digital humanities",
author = "Hiippala, Tuomo and Hotti, Helmiina and Suviranta, Rosa",
booktitle = "Proceedings of the 6th Joint SIGHUM Workshop on Computational Linguistics for Cultural Heritage, Social Sciences, Humanities and Literature",
month = oct,
year = "2022",
address = "Gyeongju, Republic of Korea",
publisher = "International Conference on Computational Linguistics",
url = "https://aclanthology.org/2022.latechclfl-1.2",
pages = "7--12",
abstract = "This system demonstration paper describes ongoing work on a tool for fair and reproducible use of paid crowdsourcing in the digital humanities. Paid crowdsourcing is widely used in natural language processing and computer vision, but has been rarely applied in the digital humanities due to ethical concerns. We discuss concerns associated with paid crowdsourcing and describe how we seek to mitigate them in designing the tool and crowdsourcing pipelines. We demonstrate how the tool may be used to create annotations for diagrams, a complex mode of expression whose description requires human input.",
}
You can install the tool from PyPI using the following command: pip install abulafia
Alternatively, you can clone this repository and install the tool locally. Move to the directory that contains the repository and type: pip install .
See the directory examples for documentation and practical examples.
To deploy your crowdsourcing tasks to Toloka, the tool needs to read your credentials from a JSON file e.g. creds.json. Never add this file to version control.
The file must contain the following key/value pairs in JSON:
{
"token": "YOUR_OAUTH_TOKEN",
"mode": "SANDBOX"
}
When you have tested your tasks in the Toloka sandbox, change the value for "mode" from "SANDBOX" to "PRODUCTION" to deploy the tasks on Toloka.
The screenshot below illustrates tool in action.
If you have questions about the tool, feel free to contact tuomo.hiippala (at) helsinki.fi or open an issue on GitHub.
FAQs
A tool for fair and reproducible crowdsourcing using Toloka
We found that abulafia demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Research
The Socket Research Team breaks down a malicious wrapper package that uses obfuscation to harvest credentials and exfiltrate sensitive data.

Research
Security News
Attackers used a malicious npm package typosquatting a popular ESLint plugin to steal sensitive data, execute commands, and exploit developer systems.

Security News
The Ultralytics' PyPI Package was compromised four times in one weekend through GitHub Actions cache poisoning and failure to rotate previously compromised API tokens.