The goal of this project is to provide neural network architectures for traffic classification and their pre-trained weights.
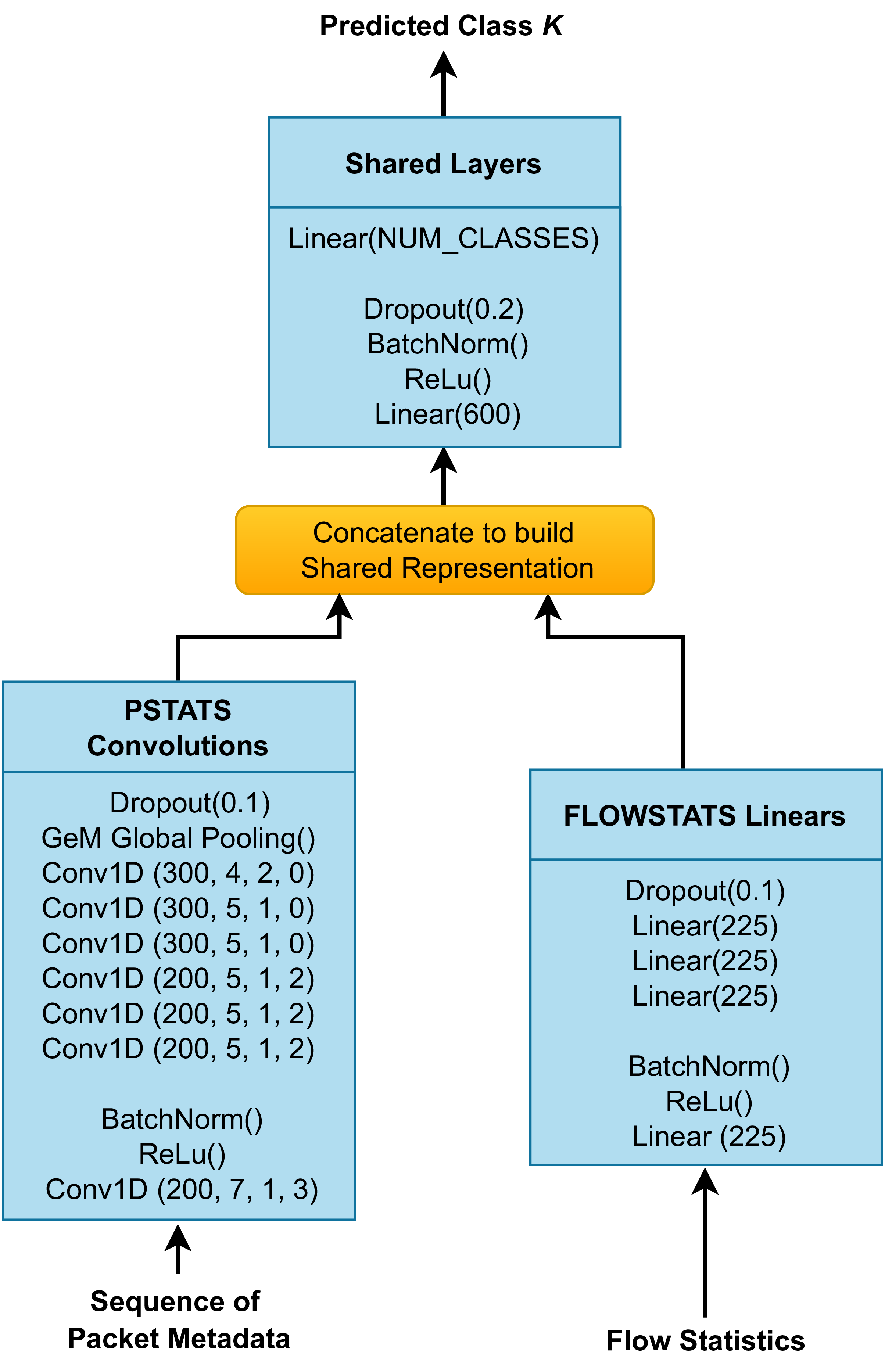
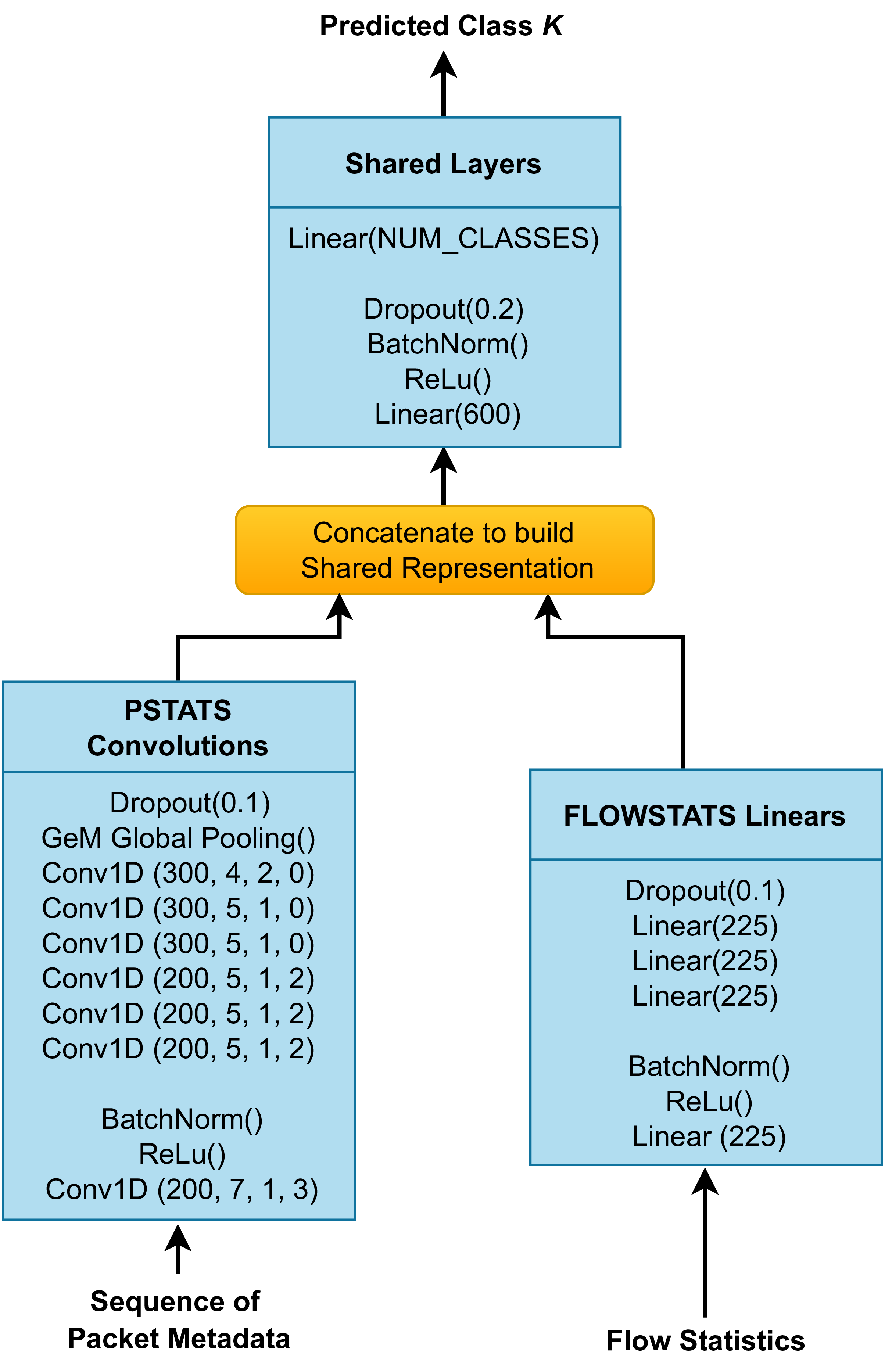
The newest network architecture is named Multi-modal CESNET v2 (mm-CESNET-v2) and is visualized in the following picture. See the getting started page and models reference for more information.
:frog: :frog: See a related project CESNET DataZoo providing large TLS and QUIC traffic datasets. :frog: :frog:
:notebook: :notebook: Example Jupyter notebooks are included in a separate CESNET Traffic Classification Examples repo. :notebook: :notebook:
Multi-modal CESNET v2
Installation
Install the package from pip with:
pip install cesnet-models
or for editable install with:
pip install -e git+https://github.com/CESNET/cesnet-models
Papers
Models from the following papers are included: