
Security News
38% of CISOs Fear They’re Not Moving Fast Enough on AI
CISOs are racing to adopt AI for cybersecurity, but hurdles in budgets and governance may leave some falling behind in the fight against cyber threats.
A pytest plugin that provides a mock NETCONF (RFC6241/RFC6242) server for local testing.
A pytest plugin that provides a mock NETCONF (RFC6241/RFC6242) server for local testing.
pytest-netconf is authored by Adam Kirchberger, governed as a benevolent dictatorship, and distributed under license.
Testing NETCONF devices has traditionally required maintaining labs with multiple vendor devices which can be complex and resource-intensive. Additionally, spinning up virtual devices for testing purposes is often time-consuming and too slow for CICD pipelines. This plugin provides a convenient way to mock the behavior and responses of these NETCONF devices.
The clients below have been tested
ncclient :white_check_mark:netconf-client :white_check_mark:scrapli-netconf :white_check_mark:Install using pip install pytest-netconf or poetry add --group dev pytest-netconf
The plugin will install a pytest fixture named netconf_server, which will start an SSH server with settings you provide, and only reply to requests which you define with corresponding responses.
For more use cases see examples
# Configure server settings
netconf_server.username = None # allow any username
netconf_server.password = None # allow any password
netconf_server.port = 8830 # default value
# Configure a request and response
netconf_server.expect_request(
'<?xml version="1.0" encoding="UTF-8"?>'
'<nc:rpc xmlns:nc="urn:ietf:params:xml:ns:netconf:base:1.0" message-id="{message_id}">'
"<nc:get-config><nc:source><nc:running/></nc:source></nc:get-config>"
"</nc:rpc>"
).respond_with(
"""
<?xml version="1.0" encoding="UTF-8"?>
<rpc-reply message-id="{message_id}"
xmlns="urn:ietf:params:xml:ns:netconf:base:1.0">
<data>
<interfaces>
<interface>
<name>eth0</name>
</interface>
</interfaces>
</data>
</rpc-reply>
"""
)
from pytest_netconf import NetconfServer
from ncclient import manager
def test_netconf_get_config(
netconf_server: NetconfServer,
):
# GIVEN server request and response
netconf_server.expect_request(
'<?xml version="1.0" encoding="UTF-8"?>'
'<nc:rpc xmlns:nc="urn:ietf:params:xml:ns:netconf:base:1.0" message-id="{message_id}">'
"<nc:get-config><nc:source><nc:running/></nc:source></nc:get-config>"
"</nc:rpc>"
).respond_with(
"""
<?xml version="1.0" encoding="UTF-8"?>
<rpc-reply message-id="{message_id}"
xmlns="urn:ietf:params:xml:ns:netconf:base:1.0">
<data>
<interfaces>
<interface>
<name>eth0</name>
</interface>
</interfaces>
</data>
</rpc-reply>"""
)
# WHEN fetching rpc response from server
with manager.connect(
host="localhost",
port=8830,
username="admin",
password="admin",
hostkey_verify=False,
) as m:
response = m.get_config(source="running").data_xml
# THEN expect response
assert (
"""
<interfaces>
<interface>
<name>eth0</name>
</interface>
</interfaces>
"""
in response
)
from pytest_netconf import NetconfServer
from ncclient import manager
from ncclient.transport.errors import AuthenticationError
def test_netconf_auth_fail(
netconf_server: NetconfServer,
):
# GIVEN username and password have been defined
netconf_server.username = "admin"
netconf_server.password = "password"
# WHEN connecting using wrong credentials
with pytest.raises(AuthenticationError) as error:
with manager.connect(
host="localhost",
port=8830,
username="foo",
password="bar",
hostkey_verify=False,
):
...
# THEN expect error
assert error
from pytest_netconf import NetconfServer
from ncclient import manager
def test_netconf_capabilities(
netconf_server: NetconfServer,
):
# GIVEN extra capabilities
netconf_server.capabilities.append("urn:ietf:params:netconf:capability:foo:1.1")
netconf_server.capabilities.append("urn:ietf:params:netconf:capability:bar:1.1")
# WHEN receiving server capabilities
with manager.connect(
host="localhost",
port=8830,
username="admin",
password="admin",
hostkey_verify=False,
) as m:
server_capabilities = m.server_capabilities
# THEN expect to see capabilities
assert "urn:ietf:params:netconf:capability:foo:1.1" in server_capabilities
assert "urn:ietf:params:netconf:capability:bar:1.1" in server_capabilities
from pytest_netconf import NetconfServer
from ncclient import manager
from ncclient.transport.errors import TransportError
def test_netconf_server_disconnect(
netconf_server: NetconfServer,
):
# GIVEN netconf connection
with pytest.raises(TransportError) as error:
with manager.connect(
host="localhost",
port=8830,
username="admin",
password="admin",
hostkey_verify=False,
) as m:
pass
# WHEN server stops
netconf_server.stop()
# THEN expect error
assert str(error.value) == "Not connected to NETCONF server"
from pytest_netconf import NetconfServer
from ncclient import manager
def test_netconf_key_auth(
netconf_server: NetconfServer,
):
# GIVEN SSH username and authorized key
netconf_server.username = "admin"
netconf_server.authorized_key = "ssh-rsa AAAAB3NzaC1yc..."
# WHEN connecting using key credentials
with manager.connect(
host="localhost",
port=8830,
username="admin",
key_filename=key_filepath,
hostkey_verify=False,
) as m:
# THEN expect to be connected
assert m.connected
Releases will follow semantic versioning (major.minor.patch). Before 1.0.0 breaking changes can be included in a minor release, therefore we highly recommend pinning this package.
Suggest a feature or report a bug. Read our developer guide.
pytest-netconf is distributed under the Apache 2.0 license.
FAQs
A pytest plugin that provides a mock NETCONF (RFC6241/RFC6242) server for local testing.
We found that pytest-netconf demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

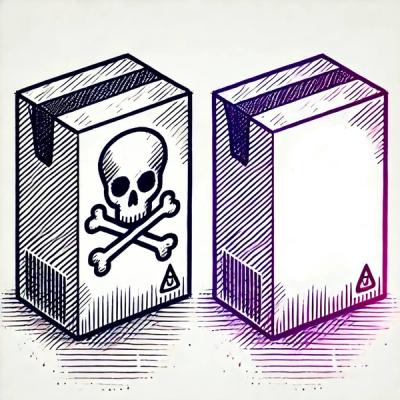
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
CISOs are racing to adopt AI for cybersecurity, but hurdles in budgets and governance may leave some falling behind in the fight against cyber threats.
Research
Security News
Socket researchers uncovered a backdoored typosquat of BoltDB in the Go ecosystem, exploiting Go Module Proxy caching to persist undetected for years.

Security News
Company News
Socket is joining TC54 to help develop standards for software supply chain security, contributing to the evolution of SBOMs, CycloneDX, and Package URL specifications.