
Security News
Research
Data Theft Repackaged: A Case Study in Malicious Wrapper Packages on npm
The Socket Research Team breaks down a malicious wrapper package that uses obfuscation to harvest credentials and exfiltrate sensitive data.
An authorization library that supports access control models like ACL, RBAC, ABAC in Node.JS
News: still worry about how to write the correct node-Casbin policy? Casbin online editor is coming to help! Try it at: http://casbin.org/editor/

node-Casbin is a powerful and efficient open-source access control library for Node.JS projects. It provides support for enforcing authorization based on various access control models.
 |  |  |  |
|---|---|---|---|
| Casbin | jCasbin | node-Casbin | PHP-Casbin |
| production-ready | production-ready | production-ready | production-ready |
npm install casbin --save
Initialize a new node-Casbin enforcer with a model file and a policy file:
import casbin from 'casbin';
const enforcer = await casbin.newEnforcer('path/to/model.conf', 'path/to/policy.csv');
Note: you can also initialize an enforcer with policy in DB instead of file, see Persistence section for details.
Add an enforcement hook into your code right before the access happens:
const sub = 'alice'; // the user that wants to access a resource.
const obj = 'data1'; // the resource that is going to be accessed.
const act = 'read'; // the operation that the user performs on the resource.
if (enforcer.enforce(sub, obj, act) == true) {
// permit alice to read data1
} else {
// deny the request, show an error
}
Besides the static policy file, node-Casbin also provides API for permission management at run-time. For example, You can get all the roles assigned to a user as below:
const roles = enforcer.getRoles('alice');
See Policy management APIs for more usage.
Please refer to the src/test package for more usage.
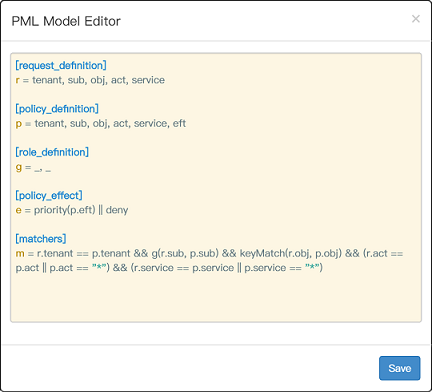
write-article, read-log. It doesn't control the access to a specific article or log.resource.Owner can be used to get the attribute for a resource./res/*, /res/:id and HTTP methods like GET, POST, PUT, DELETE.In node-Casbin, an access control model is abstracted into a CONF file based on the PERM metamodel (Policy, Effect, Request, Matchers). So switching or upgrading the authorization mechanism for a project is just as simple as modifying a configuration. You can customize your own access control model by combining the available models. For example, you can get RBAC roles and ABAC attributes together inside one model and share one set of policy rules.
The most basic and simplest model in node-Casbin is ACL. ACL's model CONF is:
# Request definition
[request_definition]
r = sub, obj, act
# Policy definition
[policy_definition]
p = sub, obj, act
# Policy effect
[policy_effect]
e = some(where (p.eft == allow))
# Matchers
[matchers]
m = r.sub == p.sub && r.obj == p.obj && r.act == p.act
An example policy for ACL model is like:
p, alice, data1, read
p, bob, data2, write
It means:
What node-Casbin does:
{subject, object, action} form or a customized form as you defined, both allow and deny authorizations are supported.root or administrator. A superuser can do anything without explict permissions.keyMatch can map a resource key /foo/bar to the pattern /foo*.What node-Casbin does NOT do:
username and password when a user logs in)https://casbin.org/docs/en/overview
You can also use the online editor (http://casbin.org/editor/) to write your node-Casbin model and policy in your web browser. It provides functionality such as syntax highlighting and code completion, just like an IDE for a programming language.
https://casbin.org/docs/en/tutorials
node-Casbin provides two sets of APIs to manage permissions:
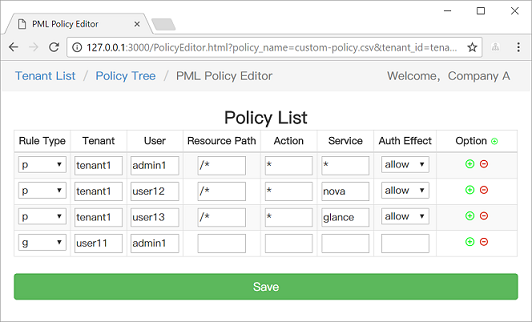
We also provide a web-based UI for model management and policy management:
In node-Casbin, the policy storage is implemented as an adapter (aka middleware for node-Casbin). To keep light-weight, we don't put adapter code in the main library (except the default file adapter). A complete list of node-Casbin adapters is provided as below. Any 3rd-party contribution on a new adapter is welcomed, please inform us and I will put it in this list:)
| Adapter | Type | Author | Description |
|---|---|---|---|
| File Adapter (built-in) | File | node-Casbin | Persistence for .CSV (Comma-Separated Values) files |
| Sequelize Adapter | ORM | node-Casbin | MySQL, PostgreSQL, SQLite, Microsoft SQL Server are supported by Sequelize |
| Waterline Adapter | ORM | node-Casbin | MySQL, MongoDB, neDB, Postgres are supported by Waterline |
| TypeORM Adapter | ORM | node-Casbin | MySQL, PostgreSQL, MariaDB, SQLite, MS SQL Server, Oracle, WebSQL, MongoDB are supported by TypeORM |
| Mongoose Adapter | ORM | @szy0syz | MongoDB is supported by Mongoose |
For details of adapters, please refer to the documentation: https://github.com/casbin/casbin/wiki/Policy-persistence
The role manager is used to manage the RBAC role hierarchy (user-role mapping) in node-Casbin. A role manager can retrieve the role data from node-Casbin policy rules or external sources such as LDAP, Okta, Auth0, Azure AD, etc. We support different implementations of a role manager. To keep light-weight, we don't put role manager code in the main library (except the default role manager). A complete list of node-Casbin role managers is provided as below. Any 3rd-party contribution on a new role manager is welcomed, please inform us and I will put it in this list:)
| Role manager | Author | Description |
|---|---|---|
| Default Role Manager (built-in) | node-Casbin | Supports role hierarchy stored in node-Casbin policy |
For developers: all role managers must implement the RoleManager interface. Default Role Manager can be used as a reference implementation.
| Model | Model file | Policy file |
|---|---|---|
| ACL | basic_model.conf | basic_policy.csv |
| ACL with superuser | basic_model_with_root.conf | basic_policy.csv |
| ACL without users | basic_model_without_users.conf | basic_policy_without_users.csv |
| ACL without resources | basic_model_without_resources.conf | basic_policy_without_resources.csv |
| RBAC | rbac_model.conf | rbac_policy.csv |
| RBAC with resource roles | rbac_model_with_resource_roles.conf | rbac_policy_with_resource_roles.csv |
| RBAC with domains/tenants | rbac_model_with_domains.conf | rbac_policy_with_domains.csv |
| ABAC | abac_model.conf | N/A |
| RESTful | keymatch_model.conf | keymatch_policy.csv |
| Deny-override | rbac_model_with_deny.conf | rbac_policy_with_deny.csv |
| Priority | priority_model.conf | priority_policy.csv |
This project is licensed under the Apache 2.0 license.
If you have any issues or feature requests, please contact us. PR is welcomed.
FAQs
An authorization library that supports access control models like ACL, RBAC, ABAC in Node.JS
The npm package casbin receives a total of 51,531 weekly downloads. As such, casbin popularity was classified as popular.
We found that casbin demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 2 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Research
The Socket Research Team breaks down a malicious wrapper package that uses obfuscation to harvest credentials and exfiltrate sensitive data.

Research
Security News
Attackers used a malicious npm package typosquatting a popular ESLint plugin to steal sensitive data, execute commands, and exploit developer systems.

Security News
The Ultralytics' PyPI Package was compromised four times in one weekend through GitHub Actions cache poisoning and failure to rotate previously compromised API tokens.