clog
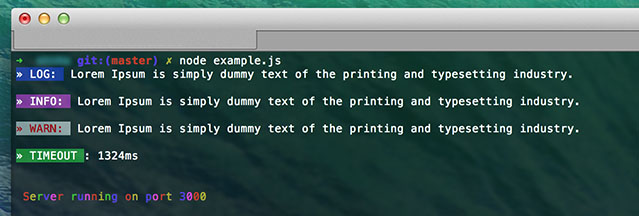
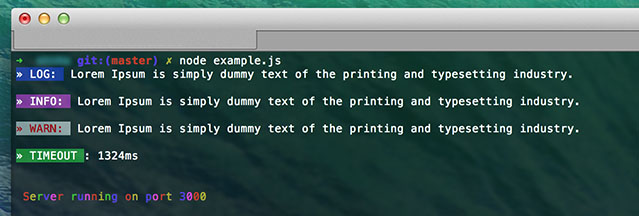
Pretty colorful cli logger for NodeJS(with table, success and more...)

#Installing
###git
$ git clone https://github.com/a8m/clog.git
###npm
$ npm install c-log --save
#Usage
var clog = require('c-log');
logger.log("Lorem Ipsum...");
logger.info("Lorem Ipsum...");
logger.warn("Lorem Ipsum ..");
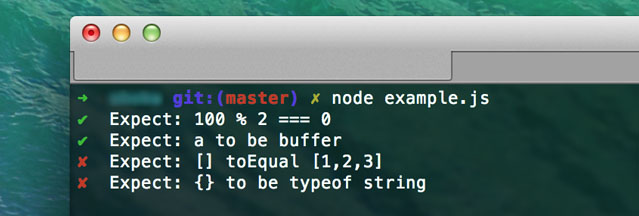
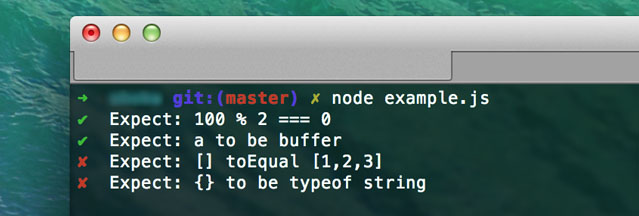
function assert(expect, msg) {
return expect
? clog.success(msg)
: clog.error(msg);
}
clog.time("fsRead");
setTimeout(function(){
logger.timeEnd("fsRead")
},2000);
var persons = [
{ name: 'Doris Fox', age: 20, isActive: false, balance: '$3,128.12' },
{ name: 'Mike Loks', age: 32, isActive: true, balance: '$12,132.1' },
{ name: 'Arle Sher', age: 12, isActive: false, balance: '$2,968.83' }
];
clog.table(persons);
╔═════════╤═══════════╤═════╤══════════╤═══════════╗
║ (index) │ name │ age │ isActive │ balance ║
╟─────────┼───────────┼─────┼──────────┼───────────╢
║ 0 │ Doris Fox │ 20 │ false │ $3,128.12 ║
╟─────────┼───────────┼─────┼──────────┼───────────╢
║ 1 │ Mike Loks │ 32 │ true │ $12,132.1 ║
╟─────────┼───────────┼─────┼──────────┼───────────╢
║ 2 │ Arle Sher │ 12 │ false │ $2,968.83 ║
╚═════════╧═══════════╧═════╧══════════╧═══════════╝
#License
MIT <3